Sunbird has been promising iMessage support on Android for about a year now. Now, with the launch of Nothing Chats built into Sunbird, the privacy dream is coming true – not just the app. No End-to-end encrypted as promised, but other users’ image files Beautiful Easy to access in plain text.
Sunbird’s promise and nothing chats is to bring iMessage support to Android. This is done by having users log in to their Apple ID through an application that routes the login through a Mac server farm. It’s not a unique method, but the big difference here is that Sunbird has made a big deal out of claiming to have end-to-end encryption throughout the entire process.
On the Sunbird Website It directly states:
Sunbird servers do not store user data promoting a safe, secure and private messaging environment. With end-to-end encrypted, confidential messaging, Sunbird is completely secure and completely private.
By adding encryption between Android and iMessage, Sunbird is the first to provide Android users with a unified and secure messaging experience.
Nothing reiterates this Landing page For nothing chats, say:
…there are no chats built into Sunbird’s platform, and all chat messages are end-to-end encrypted, meaning neither we nor Sunbird can access the messages you send and receive.
But, that alone is not true.
Alarming new findings reveal that Sunbird and Nothing chats are not, in fact, fully end-to-end encrypted, as user data is accessible in plain text.
Posted on Twitter/X by “Wukko”. Nothing Chats sends all media links, including user images, to Sentry with links to those links visible in plain text. Also, “all” data is sent and stored by Firebase and is completely unencrypted.
9to5Google Vukow’s findings can be independently confirmed.
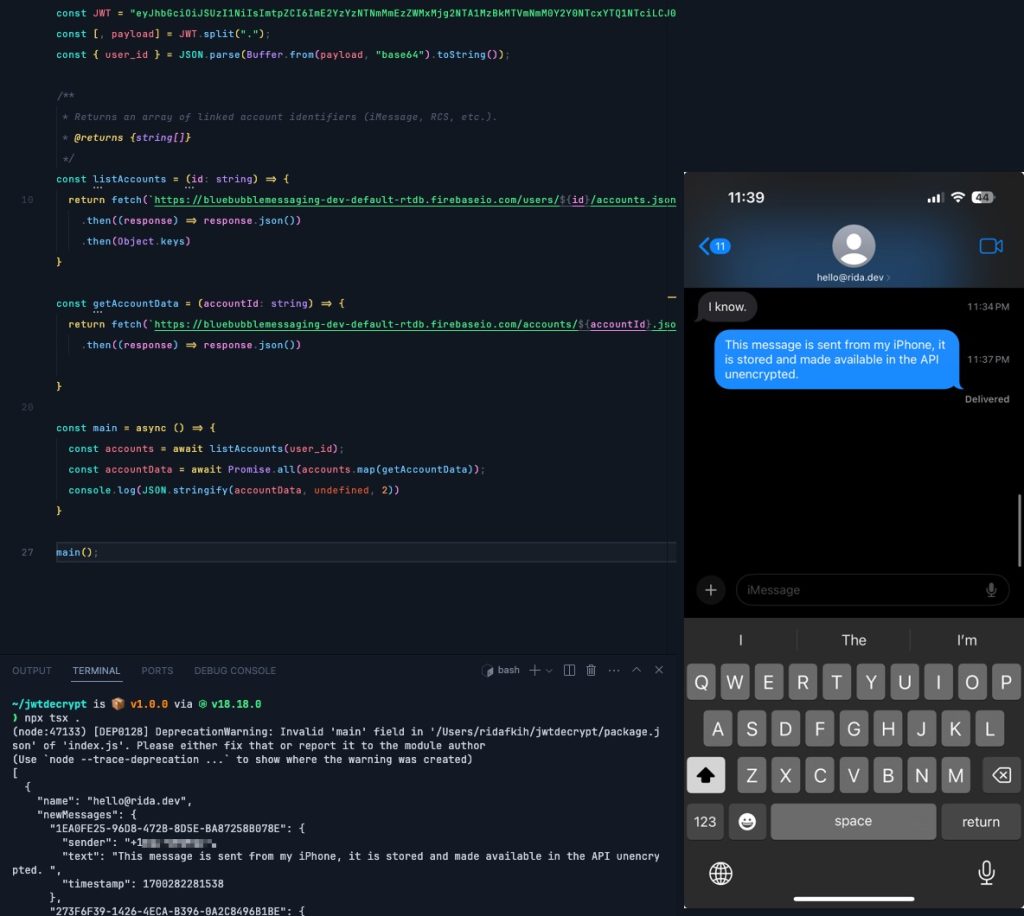
In our Dylan Roussel’s research, once a user authenticates insecure JSON Web Tokens (JWT) in transit, they can access Nothing Chat’s Firebase database and view messages and files sent by other users. in real time And in plain text. He specifically calls vCards accessible because they directly contain user names, phone numbers, email addresses, and sometimes even more personal data.
mentions that 630,000 media files are currently stored Sunbird via Firebase including images, videos, PDFs, audio and more.
Dylan further explains his findings A thread on Twitter/X.
Everyone is done Texts.com And have broken down the process in detail.
A blog post indicated that a very short code would be needed to automate the process of downloading this information. A demo of an iMessage sent, with database-only “end-to-end-encrypted” text displayed in plain text, is seen below. A proof of concept was also developed and Published on Github To show how it works.
Alas.
We first discovered the privacy nightmare, for lack of a better term, late on November 17th, and due to the highly sensitive nature of this vulnerability, did not report anything immediately (through public relations, as the company did not communicate security issues) – user data is on the line here and completely insecure. A Nothing spokesperson quickly responded to our email (which is not a typical, recorded response), but due to the timing of the findings, was unable to provide a corrective statement or detail.
However, by the time we arrived, it appeared to be nothing and a sunbird may Blocked app downloads on Play Store. No chats are shown in play store search and navigation List directly On several Nothing Phone (2) units, as pictured above, the app was listed as “not available in your country” and could not be downloaded, the app became available to users in the last few hours after noon yesterday. ET.
9to5Google’s tag
As far as privacy issues go, that’s about as bad as it gets.
Not only can the image files be accessed, but Everything is out there and very easy to find. This is unimaginably horrifying to your personal data, and beyond anyone’s concern about someone accessing your Apple ID.
While it will eventually be on Sunbird as the infrastructure and nothing chats app has been developed, nothing is worryingly due diligence here. If a vulnerability like this could be discovered within 24 hours from multiple users, how come nothing was missed in the months this partnership was built? And, beyond that, will something even worse be discovered in time?
It goes without saying at this point, but you Absolutely Nothing Chats or Sunbird should be downloaded.
Dylan Roussel contributed to this article.
FTC: We use auto-affiliate links that generate income. Further.

“Total coffee junkie. Tv ninja. Unapologetic problem solver. Beer expert.”

